
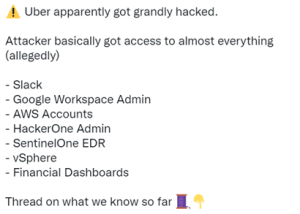
Recently, a hacker attacked Uber. After the hacker invaded Uber, he released Uber’s AWS console, HackerOne management panel, Slacke server and other screenshots, which showed that Uber may have been seriously attacked by hackers, as shown below:
Uber has also issued relevant statements, is responding to network security incidents, keeps in touch with law enforcement authorities, and will release more relevant updated information when necessary, as shown below:

According to relevant data, the hacker who attacked this time claimed that they had administrator access to corporate tools such as Amazon Web Services and Google Cloud Platform. The hacker claimed that he was only 18 years old. He invaded Uber for fun and was considering disclosing the company’s source code. After invading Uber, the hacker released relevant information to all Uber employees, but Uber employees did not know that they were attacked, Thought it was a joke.
Not long ago, Cisco has confirmed that it was attacked by Yuauowang blackmail virus and leaked some data. Fortunately, Cisco found it in time during the hacker organization’s in-depth attack. Otherwise, more core data may be leaked. We previously published a related article, Simple Analysis of Cisco’s Hacker Attacks, which has mentioned that the hacker organization has been looking for the next target, Never stop, any large enterprise may become the next target of hacker attacks.
For some information published on the Internet by Bill Demirkapi, a foreign security researcher, we also made a simple analysis of this hacker attack. In fact, this is not the first time Uber has been attacked by hackers. In 2016, Uber was attacked by hackers, which affected the personal data of 57 million users and drivers. If the information published on the Internet by the hacker organization is true, No doubt Uber has been attacked by another very serious hacker this time. I don’t know how Uber will face this attack. I have to wait for Uber to update information.
Analysis
According to the relevant information published on the Internet, the hacker carried out social work against an employee of Uber. After successfully obtaining the employee’s login certificate, he logged into the enterprise through the VPN account, and carried out horizontal scanning and penetration of the enterprise intranet. The attack process of obtaining the employee’s login certificate was restored by foreign security researchers, as shown below:
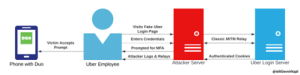
- The hacker used tools like Evilginx to set up a fake domain server to intercept Uber’s real login server and obtain the employee’s login credentials.
- After getting the employee’s login certificate, you can use the employee’s VPN access rights to access the enterprise intranet.
- After entering the enterprise intranet, the hacker just found a network sharing server inside the enterprise, which contains a PowerShell script with privileged credentials. The privileged credential information contained in the script can be used to access Uber’s DA, DUO, Onelogin, AWS, GSuite and other application systems.
If the relevant screenshot information published by the hacker is true, the hacker should have obtained many access rights to Uber, including AWS system, IAM portal, GCloud, VCenter, Slack, vSphere, and even access rights to EDR and other systems inside the enterprise. Publishing EDR screenshots from the hacker indicates that the hacker may have obtained the login credentials of Uber’s IR team members, If the hacker uses EDR to provide a “back door” for IR, and enters other employee machines of the enterprise through the “back door”, this may further expand the attacker’s access scope.
This is the end of the analysis of this attack. It can be seen that the attack process is not complicated. After all, the hacker is still young. At the same time, it can be seen from this attack that Uber’s security management and control may not be good. That way, a script containing various privileged credentials will be placed on the shared server. If all the screenshots are true, this is indeed a very serious attack, At present, the hacker has only published the relevant screenshot information for the time being, but not the specific data information, so we need to pay continuous attention to this attack later.
Through the analysis of the attack, the entry point of the hacker is still to find the employees of the enterprise to conduct targeted phishing social workers and get the login credentials of the enterprise employees. Because no enterprise can guarantee that all employees have a high degree of security awareness. In addition, social workers are highly deceptive. Any employee in the enterprise may become the target of the attack, and any employee may become the entry point for the enterprise to be attacked by hackers.
Wrap up
Targeted attacks against employees inside the enterprise, including mail phishing, puddle attacks, social engineering and other methods, are a common APT attack method used by hacker organizations. Starting with employees of the enterprise, Lazarus APT organizations have used this method for many times to phish social workers against employees of the enterprise, and then invade the enterprise server to steal relevant data. To ensure your enterprise data security, you should backup your data regularly. Vinchin offers solutions such as VMware backup for the world’s most popular virtual environments, XenServer backup, XCP-ng backup, Hyper-V backup, RHV/oVirt backup, Oracle backup, etc.
Hackers have never stopped attacking major enterprises around the world. Some APT attacks may last for several months. This targeted attack will be particularly prominent in future network security incidents. The entrance to most attacks may be just a phishing email or a corporate email address, and some leaked login credentials, Then the hacker obtains the access right to the enterprise intranet through various social work methods, and then conducts horizontal penetration until the core server of the enterprise is broken. If the enterprise can find the hacker’s attack activities in time during this process, it can conduct emergency response in the first time to reduce the enterprise’s losses.
